Internet of Things
Fixing, upgrading and patching IoT devices can be a real nightmare
Ensuring cybersecurity for computers and mobile phones is a huge, complex business. The ever-widening scope and unbelievable variety of threats...
Read more5 reasons why device makers cannot secure the IoT platform
If Akamai, Cisco and Google’s post-platform security and privacy machine learning security systems protecting the web and mobile platforms are...
Read moreToday’s property rules don’t work in our IoT world
Property and ownership are among the most basic concepts of a modern society. Our ability to clarify who owns what...
Read moreHow Microsoft’s self-soaring sailplane improves IoT, digital assistants
A machine learning project to build an autonomous sailplane that remains aloft on thermal currents is impressive enough. But the...
Read moreHelp managing IoT ranges from full-stack offerings to platform services
The tech industry’s approach to becoming a part of the IoT landscape is reminiscent of a quilting bee – a...
Read moreWhat is edge computing and how it’s changing the network
Edge computing allows data produced by internet of things (IoT) devices to be processed closer to where it is created...
Read moreFAQ: What is NB-IoT?
NB-IoT, that must stand for “no big IoT,” like “no big deal?”Awful. Why don’t you leave the jokes to me?Fine,...
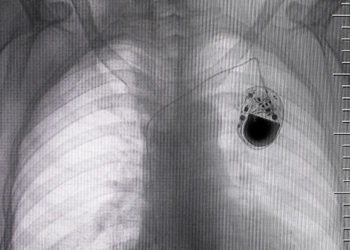
Read moreIoT poised to impact quality, capabilities of healthcare
Everything about the modern doctor’s office feels primitive. It’s one of the few businesses that requires I use my telephone...
Read morePub/Sub model could connect IoT devices without carrier networks
Three characteristics of the Internet of Things (IoT) differentiate it from industrial automation.IoT devices are inexpensive. IoT devices can be...
Read moreUp next: Disposable IoT
What if every package shipped contained a $0.20 tracker chip that could report when and approximately where the package was...
Read more